Difference Between Symmetric and Asymmetric Encryption Symmetric encryption uses a single key that needs to be shared among the people who need to receive the message while asymmetrical encryption uses a pair of public key and a private key to encrypt and decrypt messages when communicating..
People also ask, is symmetric or asymmetric encryption better?
Generally asymmetric encryption schemes are more secure because they require both a public and a private key. No. AES is more secure against cryptanalytic attacks than 512-bit RSA, even though RSA is asymmetric and AES is symmetric.
Furthermore, is AES symmetric or asymmetric? If the same key is used for both encryption and decryption, the process is said to be symmetric. If different keys are used the process is defined as asymmetric. Two of the most widely used encryption algorithms today are AES and RSA.
Simply so, what are the main differences between symmetric and asymmetric key cryptography?
The fundamental difference that distinguishes symmetric and asymmetric encryption is that symmetric encryption allows encryption and decryption of the message with the same key. On the other hand, asymmetric encryption uses the public key for the encryption, and a private key is used for decryption.
Is Caesar cipher symmetric or asymmetric?
Basically, in a symmetric cryptosytem, the sender and receiver use the same key to encrypt and decrypt the message. The Caesar cipher described above is a good example of this: both the sender and receiver use the key of three when encrypting and decrypting the message.
Related Question Answers
What is asymmetric encryption used for?
Asymmetric cryptography, also known as public key cryptography, uses public and private keys to encrypt and decrypt data. Either of the keys can be used to encrypt a message; the opposite key from the one used to encrypt the message is used for decryption.Is IPsec symmetric or asymmetric?
The real answer is that both are used. IPsec and SSL use asymmetric encryption to establish the encryption protocol when the session starts and then to securely exchange a private key used during the session. This private key is similar to the single secret key used in symmetric encryption.What is the biggest problem with symmetric key encryption?
The biggest problem with symmetric key encryption is that you need to have a way to get the key to the party with whom you are sharing data. Encryption keys aren't simple strings of text like passwords. They are essentially blocks of gibberish. As such, you'll need to have a safe way to get the key to the other party.What are the advantages of asymmetric over symmetric encryption?
The main advantage of symmetric encryption over asymmetric encryption is that it is fast and efficient for large amounts of data; the disadvantage is the need to keep the key secret - this can be especially challenging where encryption and decryption take place in different locations, requiring the key to be movedIs Blowfish symmetric or asymmetric?
Blowfish is an encryption algorithm that can be used as a replacement for the DES or IDEA algorithms. It is a symmetric (that is, a secret or private key) block cipher that uses a variable-length key, from 32 bits to 448 bits, making it useful for both domestic and exportable use.Which three types of encryption are asymmetric?
[Review] 3 Main Types of Encryption: Hash, Symmetric, Asymmetric.Is Diffie Hellman symmetric or asymmetric?
Diffie Hellman uses a private-public key pair to establish a shared secret, typically a symmetric key. DH is not a symmetric algorithm – it is an asymmetric algorithm used to establish a shared secret for a symmetric key algorithm.Is TLS symmetric or asymmetric?
TLS, also known as SSL, is a protocol for encrypting communications over a network. TLS uses both asymmetric encryption and symmetric encryption.Which cryptographic is faster?
Symmetric key encryption doesn't require as many CPU cycles as asymmetric key encryption, so you can say it's generally faster. Thus, when it comes to speed, symmetric trumps asymmetric.Where is symmetric encryption used?
Some examples of where symmetric cryptography is used are: Payment applications, such as card transactions where PII needs to be protected to prevent identity theft or fraudulent charges. Validations to confirm that the sender of a message is who he claims to be. Random number generation or hashing.What does 3des stand for?
Introduced in 1998, 3DES, also known as Triple DES, Triple DEA, TDEA, or the Triple Data Encryption Algorithm, is a cryptographic cipher. It is a symmetric key block cipher, meaning that the same key is used to encrypt and decrypt data in fixed-length groups of bits called blocks.What is secret key cryptography?
A secret key is the piece of information or parameter that is used to encrypt and decrypt messages in a symmetric, or secret-key, encryption. In assymetric encryption, two separate keys are used. One is a public key and the other is a secret key.How are symmetric and asymmetric keys used together?
Asymmetric and symmetric encryption are typically used together: use an asymmetric algorithm such as RSA to securely send someone an AES (symmetric) key. The symmetric key is called the session key; a new session key may be retransmitted periodically via RSA. This approach leverages the strengths of both cryptosystems.What is symmetric and asymmetric multiprocessing?
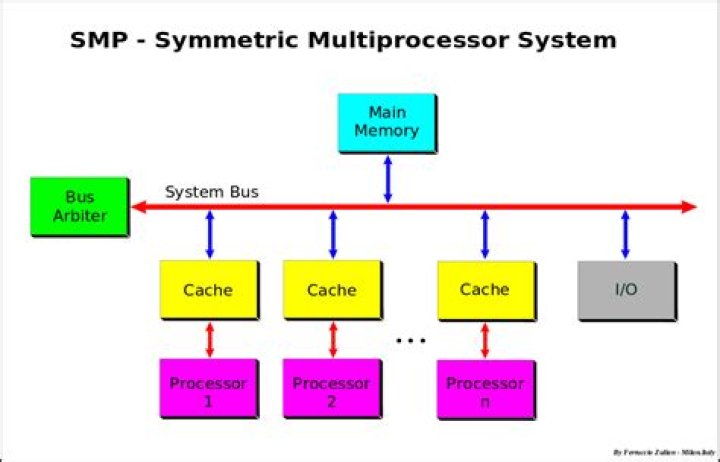
The main difference between symmetric and asymmetric multiprocessing is that, in symmetric multiprocessing, the CPUs are identical and they share the main memory while, in asymmetric multiprocessing, the CPUs are not identical and they follow slave-master relationship.What do you mean by public key?
In cryptography, a public key is a large numerical value that is used to encrypt data. In asymmetric cryptography, whatever is encrypted with a public key may only be decrypted by its corresponding private key and vice versa.What do you mean by symmetric encryption?
Symmetric encryption is an encryption methodology that uses a single key to encrypt (encode) and decrypt (decode) data. It is the oldest and most well-known technique for encryption. The secret key can be a word, a number, or a string of letters, and it's applied to a message.Is ECC symmetric or asymmetric?
ECC is an approach — a set of algorithms for key generation, encryption and decryption — to doing asymmetric cryptography. Asymmetric cryptographic algorithms have the property that you do not use a single key — as in symmetric cryptographic algorithms such as AES — but a key pair.What is asymmetric system?
In telecommunications, the term asymmetric (also asymmetrical or non-symmetrical) refers to any system in which the data speed or quantity differs in one direction as compared with the other direction, averaged over time.Has AES 256 been cracked?
AES-256 is indeed cracked, because it doesn't hold its original 256bit security. You ask if it is secure - security isn't a yes/no question, it is 231bit secure, and common wisdom is that 128bit+ is "pretty secure", and 90bit- is close to practically broken.