.
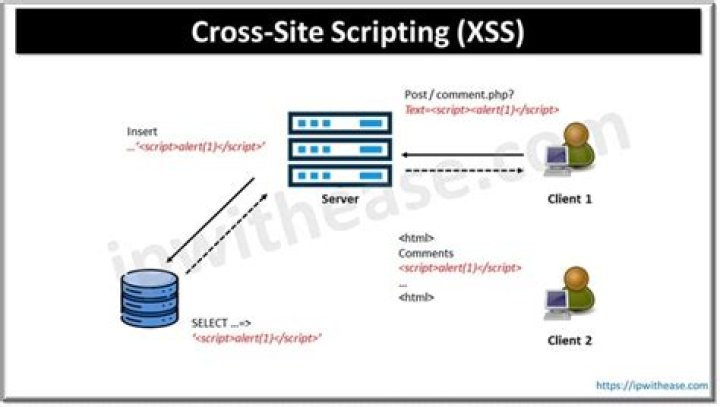
Subsequently, one may also ask, what is Cross Site Scripting example?
Overview. Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user.
Beside above, what is cross site scripting and how can it be prevented? The first method you can and should use to prevent XSS vulnerabilities from appearing in your applications is by escaping user input. By escaping user input, key characters in the data received by a web page will be prevented from being interpreted in any malicious way.
Subsequently, one may also ask, what is the difference between persistent and non persistent cross site scripting attacks?
Non-persistent XSS - the main difference is that a web application doesn't store the malicious input in the database. A special case of non-persistent XSS is called - this type of attack is done without sending any DOM-based XSS requests to the web server. The attacker injects JavaScript code directly.
How does cross site scripting work?
Cross-site scripting works by manipulating a vulnerable web site so that it returns malicious JavaScript to users. When the malicious code executes inside a victim's browser, the attacker can fully compromise their interaction with the application.
Related Question AnswersWhat are the types of cross site scripting?
There are three major types of XSS attacks:- Persistent XSS, where the malicious input originates from the website's database.
- Reflected XSS, where the malicious input originates from the victim's request.
- DOM-based XSS, where the vulnerability is in the client-side code rather than the server-side code.
Why is it called cross site scripting?
The expression "cross-site scripting" originally referred to the act of loading the attacked, third-party web application from an unrelated attack-site, in a manner that executes a fragment of JavaScript prepared by the attacker in the security context of the targeted domain (taking advantage of a reflected or non-What is CSRF attack example?
It can result in damaged client relationships, unauthorized fund transfers, changed passwords and data theft—including stolen session cookies. CSRFs are typically conducted using malicious social engineering, such as an email or link that tricks the victim into sending a forged request to a server.What is SQL injection attack with example?
SQL lets you select and output data from the database. An SQL Injection vulnerability could allow the attacker to gain complete access to all data in a database server. For example, in a financial application, an attacker could use SQL Injection to alter balances, void transactions, or transfer money to their account.What is the difference between XSS and CSRF?
Fundamental difference is that CSRF (Cross-site Request forgery) happens in authenticated sessions when the server trusts the user/browser, while XSS (Cross-Site scripting) doesn't need an authenticated session and can be exploited when the vulnerable website doesn't do the basics of validating or escaping input.What is a cross site scripting attack and how does it work?
Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user.Why is cross site scripting dangerous?
Stored cross-site scripting is very dangerous for a number of reasons: The payload is not visible for the browser's XSS filter. Users might accidentally trigger the payload if they visit the affected page, while a crafted url or specific form inputs would be required for exploiting reflected XSS.What is reflected cross site scripting?
Reflected Cross-site Scripting (XSS) occur when an attacker injects browser executable code within a single HTTP response. The injected attack is not stored within the application itself; it is non-persistent and only impacts users who open a maliciously crafted link or third-party web page.What are the two types of cross site attacks?
Types of XSS: Stored XSS, Reflected XSS and DOM-based XSS- Stored XSS (Persistent XSS) The most damaging type of XSS is Stored XSS (Persistent XSS).
- Reflected XSS (Non-persistent XSS) The second and the most common type of XSS is Reflected XSS (Non-persistent XSS).
- DOM-based XSS.
- XSS Discovery and Prevention.
What is blind XSS?
Blind XSS is a flavor of cross site scripting (XSS), where the attacker “blindly” deploys a series of malicious payloads on web pages that are likely to save them to a persistent state (like in a database, or in a log file).Is XSS client or server side?
XSS attacks are generally stored in your database and distributed through your system to your clients. Filtering on XSS attacks should be done on user input, You generally should not accept any type of Javascript input. Its a server-side vulnerability that can be exploited via client-side applications.What are the common defenses against XSS?
5 Answers- Specifying a charset.
- HTML escaping.
- Other types of escaping.
- Validating URLs and CSS values.
- Not allowing user-provided HTML.
- Preventing DOM-based XSS.